PC User Monitoring Software: Orvell Monitoring 8.2 24/7 global customer support. No subscriptions or recurring fees.
Orvell Monitoring – Spy Software

Invisibly Monitor Chats, Emails, Program- and Website Activities, Keystrokes and more. Learn what your child or employee does on your computer today!
Orvell Monitoring has been an award-winning, cutting-edge spy software solution for over 22 years! Over a decade of refinement has created an incredibly easy-to-use computer monitoring solution.
The powerful features of Orvell Monitoring make investigations quick and efficient. Easy to install. Easy to use.
Over 100 features that let you spy on computers
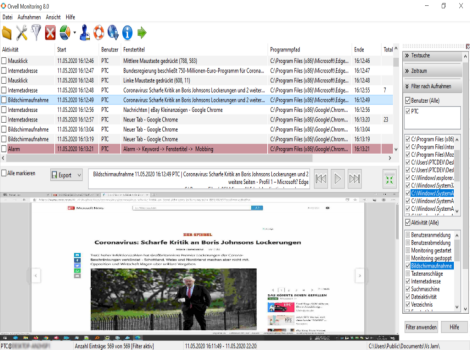
Screenshot Capturing
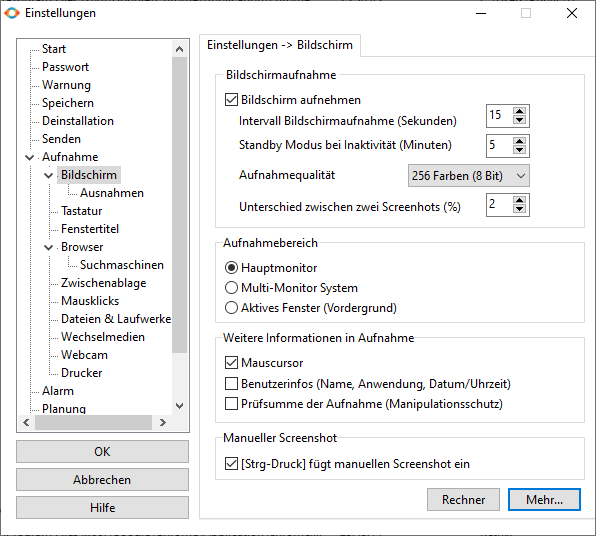
Take Snapshots Of The Desktop
More informationThe PC user monitoring software can take snapshots of your desktop at set intervals of time, whenever websites are visited, allowing you to visually see what is happening at all times. The screenshot capture manager has a built-in video-like slideshow playback for easy viewing, and screenshots are categorized by content - social networking, webmail, website usage, and more. The screenshot capturing can be configured to increase its capture frequency when window captions containing specific keywords are interacted with so vital information is not missed.
The Spy Software will stop logging when the user is inactive for a specified amount of time, when they are active again Orvell Monitoring resumes logging.
Orvell Monitoring can be configured to record activities that occur only in specific programs or windows. Activities outside of the specified programs are not recorded, allowing you to record only specific programs usage, rather than everything a user does.
Options: Recording interval
More Screenshot Recording Features
Playback
The screen recordings are called up like on a video recorder or hard disk recorder.Website Activity
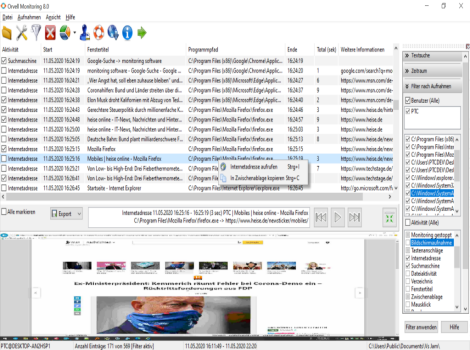
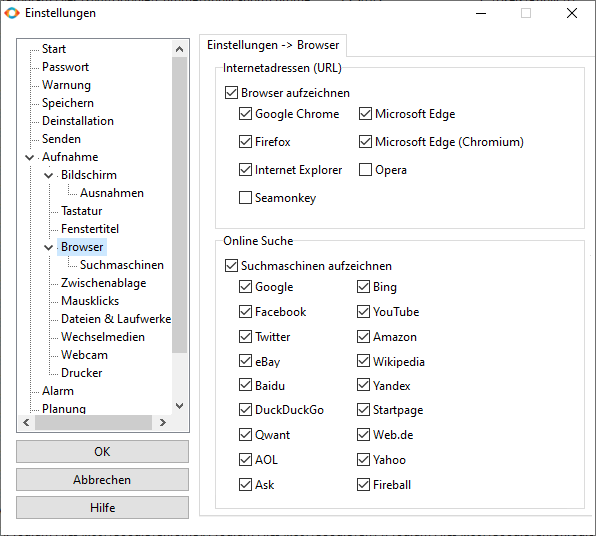
Reveals All Website Visits And What They Search
More informationLog all website visits by the popular browsers used today. All website visits are logged by website address, username, and time of the site visit. Orvell Monitoring also logs how long users visit each website so you can easily see what websites are visited the longest.
Log all online searches performed by the popular search engines used today: Google, Google Pictures, Google Videos, AOL, MSN, Yahoo, Altavista, Ask, Hotbot, A9 (Amazon), Fireball, Lycos, Web.de, MySpace, YouTube, Wikipedia, Astalavista, Torrentspy, BitTorrent, Bing, Twitter and Facebook.
Google Chrome, Firefox Quantum, Microsoft Edge, Internet Explorer, Tor, Opera and other browsers are supported.
The monitoring of the incognito mode (private browsing function) is also included.
In addition, the search terms of the popular search engines are recorded (who searched for what and where?).
Keystroke Recorder
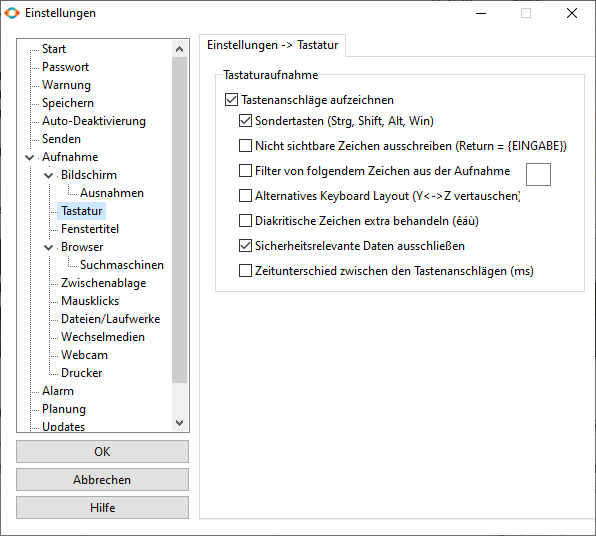
Get All Keystrokes They Type
More informationMonitor and log all keystrokes along with the window they are typed in include timestamp.
Passwords captured are flagged for easy viewing. If screenshot capturing is enabled, the Orvell Monitoring will display related screenshots alongside the keystroke log entries.
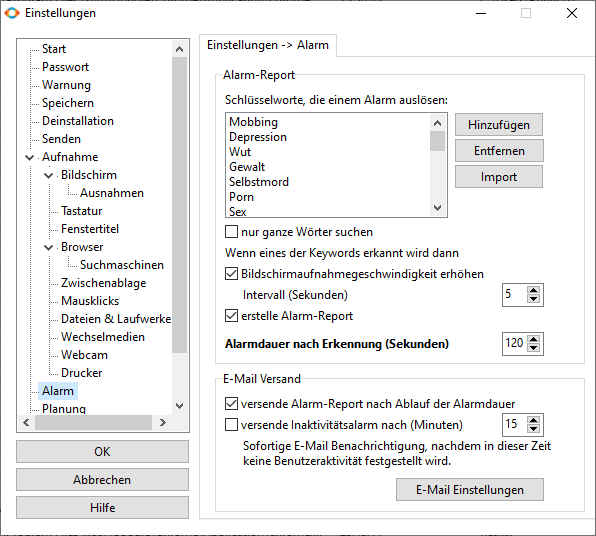
The alarm function notifies you immediately by email as soon as certain words are entered on the keyboard. For example, when an employee shares confidential information.
Special keys and key combinations are also recorded.
Important: the keylogger can also be completely deactivated so that, for example, no passwords or other security-relevant data are recorded. Otherwise, all passwords are also recorded on Facebook, Google or Twitter, among others.
Application Usage
Monitor And Log All Applications
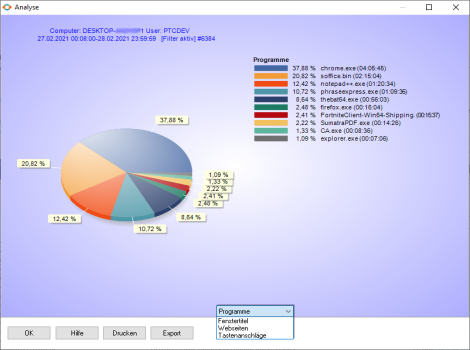
More informationMonitor and log all applications ran by users - Orvell Monitoring logs when the application was started, stopped, and how long it was actually used.
Users cannot fool Orvell Monitoring by simply opening a program and leaving it running in the background - Orvell Monitoring will know how long the program was actually used.
The following activities are evaluated:
This shows which programs on the computer are used most often by whom.
Alerts via Email
Receive Instant Behavior Alerts via Email
More informationAct quickly on questionable PC activities
The Spy Software can be configured to send you instant email notifications when a user runs an unwanted website, chat client, or application.
Alerts can also be sent when the computer is started/shutdown, when certain programs or windows are used, and even when a user types a trigger keyword!
For additional security, the PC Spy Software can send screenshots along with the notification alert email showing you exactly what they were doing when the alert was triggered.
Each of these email notifications contains the following informations:
USB Stick Monitoring: In addition to keyword recognition, the PC user monitoring software can send an email immediately when a USB stick is plugged into the PC. You will also find out which files have been copied to the USB stick. Use it to prevent data loss and data theft.
Inactivity monitoring: To recognize loss of productivity e.g. if the PC is not used for a certain period of time, a corresponding email can be sent.
Sending: You can use free email accounts (freemailer) such as Gmail, Yahoo or the company mail server to send the alarm reports.
Social Media
Record Facebook, Twitter & More
More informationGet informed about their Facebook activities: Monitor Facebook contacts, conversations and get notified about the activities going on in your child’s life. Spy on their Facebook chat to know if something is wrong. Check pictures, videos, chat of your kid's or employee's Facebook any time you wish. Spy on multimedia files to make sure that there is no point to worry about.
Only "some" time for private matters?
Log all activities by the popular Social Media platforms used today.
The intelligent Screenshot Capturing of Orvell Monitoring records every activity by the popular Social Media platforms.
Conversations
Record Emails & Chats
More informationEmail recording: Monitor and log all emails sent and received by users of your computer! Also Webmail.
Chat recording: Monitor and log both sides of all chat conversations made on chat clients with the Advanced Screenshot recording. Also Instant Messages.
All Email/Chat-Clients and Messengers (also Signal, WhatsApp) Supported!
Send recordings
Local, Network, FTP, Cloud & Email
More informationAfter the monitoring software has been installed, it records the activities on the PC in chronological order. But how do you get this?
There are many ways to get the recordings...
You can view and evaluate the archived recordings directly on the PC or via your network.
Or you can have the recordings automatically sent to wherever you are.
As soon as the reports have reached a certain size (freely adjustable), they can be transmitted automatically in the following ways:
Encryption methods such as SSL or TLS are supported. The reports can be password-protected as a ZIP archive.
Data security: In contrast to other monitoring solutions of this type, which allow the retrieval of the recordings via a website, we do not save any of your recordings on our servers! The recordings always remain under your control, as they are either saved locally on the PC or in your network or sent via your mail server.
ProtectCom does not save any data from your monitored PCs.
Fast-Installer
Invisibly Installation In Seconds
More informationIf you want, you generate a configuration file for the Fast-Installer that automatically executed during the installation. This means that manual activation or configuration of dispatch data (e.g. mail server), scope of recording, storage path, etc. is no longer necessary.
This automatic installation therefore only takes a few seconds and can be carried out completely invisibly and without user interaction!
More Features
Security, Encryption, Password Protection and more...
More informationOrvell Monitoring is undetectable under all Windows versions (it does not even show up in the task manager on any Windows platform). The PC user monitoring software has powerful lockdown and logging scheduling features, log file encryption, optional startup warnings, and much more.
The Spy Software can log just about every move a user makes - generating massive amounts of user activity information - so essential log management and reporting features.
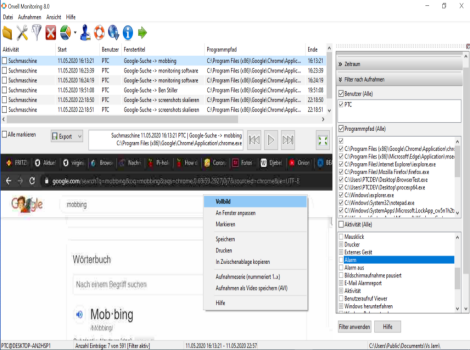
Record search terms
The advanced Internet recorder also records the search terms that have been submitted via the popular search engines. It can be seen which user searched for which terms in which search engines and when.
Files System Usage
Log all file system activity. All file modifications, creations, and deletions are logged by the time of the event, and the user who executed them. File events that take place on portable/removable drives are also recorded.
Files/Documents Accessed: Log all files opened or copied from within Windows Explorer. The log viewer provides links to the documents.
Documents Printed: Log all documents printed by users of your PC. Logs include the document printed, who printed it, what printer was used, and when.
Graphic Analysis
Orvell Monitoring creates graphical analysis of internet and computer usage with pie charts. You can see which programs and websites were used and accessed most frequently. The number of keystrokes per application can also be displayed.
Export
All recordings can export as plain Text-, CSV- or the original format. Screenshots can export export to BMP-, JPEG- (as single shot/ongoing shots) or video in AVI format.
User administration/Scheduling Time
If only the activities of certain users are to be monitored, these can be defined via the user administration. Simply enter the user name (s) concerned and from now on only these users will be recorded. Thus, for example, you do not take up your own activities. Also configure Orvell Monitoring to monitor and record only when you want it to!
Warning Screen
The optional warning message (once/repeating) reminds the user that his PC activities are being recorded (totally optional).
Automatic deactivation
Orvell Monitoring deactivates itself automatically at a certain point in time if desired.
Password Protection
Without the password, the PC monitoring software cannot be uninstalled, over-installed or reconfigured.
PC Usage Logging
Log all system shutdowns and user log-ons, as well as Orvell Monitoring actions: starting/stopping of monitoring processes, option changes, log accesses, and failed access attempts to start/stop monitoring. This also shows how long a user was active during a monitoring session.
Log how long users are active, and inactive during each computer session. The logs show when each session started, and when it ended. Log how long users were active and idle each session, and more.
AutoClear
You can set Orvell Monitoring to clear your monitoring logs every xxx days of actions logged. This provides for minimal usage of disk space. Or delete the recordings manually.
Clipboard Logging
Log all text copied to the Windows clipboard by users.
Filtering
The filter of the PC user monitoring software allows to display the recordings quickly filtered according to a specific period, user, application, activity and/or a search text. Example: a search for the text "sex" or "Facebook" only shows the recordings in which the search word appeared.
Instant Log Retrieval with a USB Stick
Orvell Monitoring allows you to quickly retrieve activity logs when time is an issue. If you only have a few moments to retrieve logs you can insert an authorized USB or portable drive into your computer which Orvell Monitoring will then copy activity reports to.
Configurable Stealth Mode Hotkey
The PC user monitoring software allows you to configure its hotkey pattern to whatever key combination you want – making it harder for others to stumble across the monitoring software!
Log File Encryption
Orvell Monitoring has a built in encryption option that allows you to have all your activity logs encrypted so others cannot stumble across the logs or read them without using the protected log viewer.
Log File Backdating
The Spy Software can be configured to backdate all log files it creates so that they appear older than they really are. This will make it impossible for users to find log files by performing system searches for most recently modified files.
Idle Timeout
Orvell Monitoring will stop logging when the user is inactive for a specified amount of time, when they are active again Orvell Monitoring resumes logging.
Stealth-Mode
The user monitoring software can run totally in stealth; that is, it is virtually undetectable to the user. Orvell Monitoring will NOT show up in the task manager under Windows – at all. Orvell Monitoring does not appear in registry and Windows startup utilities while it is running, either.
Extensive help
If you have any questions about the use or configuration of the software, our extensive support database is always just a click away. Registered users also have access to the constantly updated support help with lots of tips and assistance. In addition, our premium support from our specialists is available around the clock.
And if a problem proves to be particularly persistent, we are happy to help via Remote-Software.
With Orvell Monitoring you have a professional and powerful software for recording and analyzing all processes on a Windows PC. Easy to install and use.
Purchase nowInvisible mode
Orvell Monitoring has a very sophisticated camouflage function (i.e. it runs unnoticed in the background). If the camouflage function (stealth mode) is activated, the surveillance software is not represented by an icon, nor is it listed as an installed program under "Programs" or displayed in the taskbar.
In order to view the recordings again later or to change program settings, call up the monitoring software with the key combination (hotkey) known only to you and enter your password.
The monitoring software cannot be uninstalled, over-installed or reconfigured without your personal password.
Orvell Monitoring is the comprehensive excellent Award-winning Monitoring software for Windows PCs.
With more than 50,000 satisfied customers in over 80 countries,
Orvell Monitoring is one of the most successful programs for PC monitoring worldwide.
How can I monitor a PC?
1
BUY ORVELL MONITORING FOR PC
Make sure that the PC to be monitored is compatible with our monitoring software.
Fill out the order form and make your payment. You will receive further instructions immediately after purchase. Please also read our legal information before purchasing the software.
2
DOWNLOAD AND INSTALLATION
Download the installation file from the order email using the download link and then start it.
The wizard will guide you through the installation, which only takes seconds. The monitoring software then automatically starts to log all PC activities unnoticed in the background.
3
VIEW ALL PC ACTIVITIES
To view the recorded PC activities or to change the program settings, call up the monitoring software with the key combination (hotkey) known only to you.
This was displayed during the installation. After entering your password, you can view the recorded recordings.
Download now and start in 5 minutes!
Special: 007 USB card - only for a short time
Expand your order and receive Orvell Monitoring on our limited USB card in business / credit card format and 007 design. Usable like a USB stick.
Pre-configured with your license number for immediate installation, including automatic activation.
Storage capacity: 4 gigabytes. Design: 007 logo in glossy print.
Only while supplies last! Purchase now
Reasons to monitor PC and Networks
Protect Your Children: Computer Monitoring
Record all activities from PC, Mac, Android phone and iPhone. Find out what your child experiences on their computer and on the Internet.
Home office control: monitor productivity and working hours
Workplace control: employee activities that harm your company
Increase IT security in the company network in order to reduce costs, improve service and keep risks under control.
The Spy Software: FAQ
Answers to frequently asked questions
For a limited time, Ultimate Care is included FREE with your purchase of Ultimate Care entitles you to one full year:
Payment processing: MyCommerce/ShareIt from Cologne is our long-term partner for order and payment processing. MyCommerce/ShareIt answers questions about the ordering process here.

Security: all access to the order pages of the online shop takes place via the SSL technology (Secure Socket Layer) with our partner MyCommerce/ShareIt. All common web browsers support this technology and thus ensure that the personal data you provide during the ordering process is securely transmitted. MyCommerce/ShareIt uses Norton / Symantec technologies.
If you still not want to send your credit card details over the Internet, you can also transfer the information to our Customer service by phone or fax.

Data protection: MyCommerce/ShareIt has been awarded the TRUSTe data protection seal. This means that this Privacy Policy and TRUSTe practices have been tested for compliance with TRUSTed Cloud Program Requirements, including transparency, scope of liability and choices regarding the collection and use of your personal information.
Information on the credit card statement / account statement: on your credit card statement or wire transfer is merely MyCommerce/ShareIt listed with a purpose. The purchased software is not mentioned there.
Licensing: the software is licensed according to the number of computers to be monitored. Example: if you want to monitor one Windows-computer, a single license is sufficient. If you want to monitor 2 computers, you need a 2 license (= multiple license), etc.
When the recordings are called up via a network, the PC with the recordings are called up does not have to be licensed.
Software runtime: the software works indefinitely.
Support/Hotline: With the purchase you automatically receive the Ultimate Care / Premium Support Package including 12 months updates, support and much more.
Backup delivery: For the additional Backup delivery, choose "Backup" on the order page. In addition to the email delivery, you will also receive the software by post (plus shipping costs)!
Purchase and installation: it is not absolutely necessary that you purchase the software from the PC on which you want to use the software. After purchasing, simply copy the installation file to a USB stick and run it later on the target device.
Postal address: the postal address is required for the creation of your invoice, which will be sent to you electronically as a PDF file to your e-mail address. You will never received anything from ProtectCom or MyCommerce/ShareIt in the mail - unless you choose the additional Backup delivery.
Subscription: You dont have to buy any subscriptions or pay recurring fees.
Anti-Spam: No customer or interested party will receive unsolicited emails from us - unless you have voluntarily subscribed to our newsletter.
30 days Refund warranty: If you have technical problems with the software that cannot be resolved with the help of our customer service team, please contact us within 30 days of purchase for a full refund.
Do you have anymore questions? You get more answers in our Support area or contact us.
In contrast to other monitoring solutions of this type, which allow the retrieval of the recordings via a website, we do not save any of your recordings on our servers! The recordings always remain under your control, as they are either stored locally stored on the PC or in your network or sent via your mail server.
ProtectCom does not save any data from your monitored PCs. So we have no access to your recordings and nobody can steal this data.
The required hard disk space mainly depends on the size of the screen recordings:
A typical 8-hour day with screen recording every 30 seconds (in 256 colors) uses up approx. 50 MB of hard disk space per day.
Maintenance free: by default, the monitoring software logs the recordings of the last 30 days (freely adjustable). With 0.5 GB of hard disk space, a week of PC activities can be archived without any problems.
Contact
We are happy to support you with your individual questions and suggestions about our products.